Why Cybersecurity Needs to be Separated from IT in Local Governments
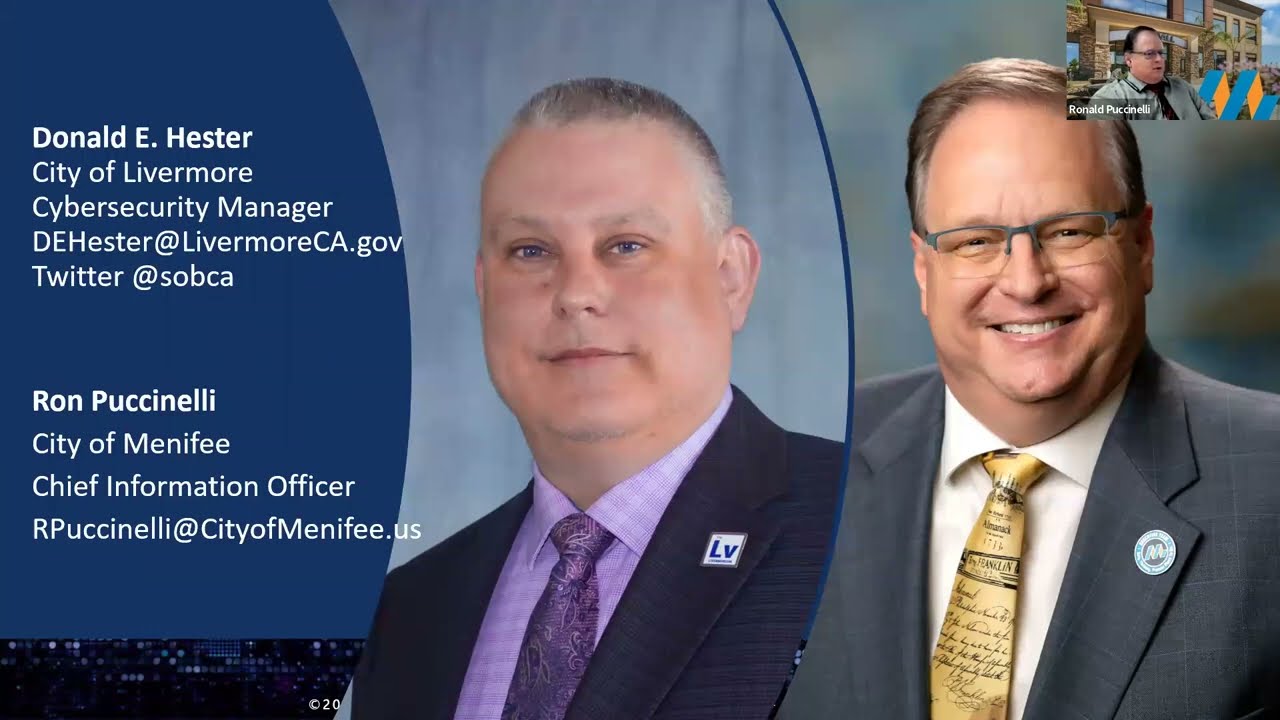
- Donald E. Hester

- Nov 10, 2021
- 7 min read
Updated: Mar 28, 2023
"The days of the CISO being completely IT-centric and as such being in a role under the CIO is gone. Managing security effectiveness and risk management transcends IT and has to operate at an executive level so that technical and non-technical decision makers can be armed with evidence-based data in order to make business decisions more effectively and efficiently from an informed position." - Brian Contos, CISO for Verodin
As an auditor, I often encountered a common question: where should cybersecurity be placed in the local government? While some may assume that it belongs in the IT department, this response fails to recognize the full extent of cybersecurity and the importance of aligning it with the organization's business objectives. Burying cybersecurity within the IT organization poses real risks that must be acknowledged.

Questions about Organizational Structure for Cybersecurity
What do you want Cybersecurity to be?
What funding is available?
Are you looking for oversight?
Are you looking for hands-on technical?
Are you looking for governance, risk, and compliance?
Are you looking for cybersecurity to be strategic, tactical, or both?
Where is the best place for the function or functions in your organization?
To begin this discussion, it is important to have a clear understanding of certain concepts. Firstly, it is essential to remember that cybersecurity is the means by which an organization responds to cyber risk. It is important to note that not all cyber risks fall under the realm of IT risks. For instance, areas such as Operational Technology (OT), elections security and disinformation, privacy, ethical use of technology (especially AI), compliance, Critical Infrastructure security, and the convergence of information and physical security are all examples of cyber risks that do not typically fall under IT but should be included in any comprehensive cybersecurity strategy.
Another important consideration is that cybersecurity is comprised of several distinct functions. It is not a single entity. While some of these functions can be effectively integrated within the IT organization for the purpose of separation of duties, others need to be located outside of the IT organization.
The Enterprise Governance of Information and Technology (EGIT) plays a vital role in ensuring that an organization's digital transformation efforts deliver value and mitigate any business risks that may arise as a result of the transformation. The IT Governance Institute defines EGIT as the coordination of efforts across the organization to ensure that technology is delivering value, and any associated risks are mitigated effectively.

"Enterprise Governance of Information and Technology (EGIT) is concerned with value delivery from digital transformation and the mitigation of business risk that results from digital transformation." - IT Governance Institute
To achieve the goals of EGIT, IT and cybersecurity must work together closely. While IT's main focus is to ensure that technology brings value to the organization, cybersecurity's main goal is to identify and address cyber risks. These goals may often conflict with each other, as innovation and risk management do not always align.
This conflict is important to keep in mind when considering where to place cybersecurity in an organization. If cybersecurity is placed under IT, the organization may prioritize innovation over cyber risk management, leaving the organization vulnerable to cyber threats. On the other hand, placing IT under cybersecurity may prioritize cyber risk management over innovation, which can hinder the organization's ability to adapt to changing technologies and remain competitive in the market.
Therefore, it is crucial to strike a balance between innovation and risk management when implementing EGIT. Organizations must ensure that both IT and cybersecurity are involved in the decision-making process and work together to identify and address any cyber risks that may arise from digital transformation. By doing so, the organization can ensure that its digital transformation efforts deliver value while mitigating any associated risks effectively.
You can see in the graphic below how the roles of CIO and CISO are separate from each other.

One common reason for organizations to place cybersecurity under IT is a lack of understanding of the different functions of cybersecurity. Many organizations mistakenly believe that cybersecurity falls solely under the realm of IT, when in reality it requires a separate and distinct set of skills and expertise as well as providing some level of oversight.
Gartner's paper, "Determining whether the CISO should report outside of IT," provides valuable insights into the different cybersecurity functions that should be separated from the CIO and placed under the CISO. These functions include policy development and enforcement, assurance that security operations are functioning as intended, compliance with regulatory and legal requirements, driving cybersecurity strategy, developing cybersecurity programs, assessing cyber risks, and providing cybersecurity awareness.
On the other hand, certain cybersecurity functions can be effectively managed under the CIO. These functions include infrastructure protection, data protection, identity and access management, security operations (monitoring), the security operations center (SOC), threat hunting and incident response as part of the SOC, and change, patch, and configuration management.
Understanding the different functions of cybersecurity is crucial when deciding where to place cybersecurity within an organization. By recognizing the importance of separating certain functions from IT and placing them under the CISO, organizations can better manage cyber risks and ensure that their digital transformation initiatives are delivering value while also mitigating potential business risks.
As digital transformation continues to shape local governments, the role of the CISO is becoming increasingly important. Unfortunately, in many local governments, the CISO is still viewed as a subordinate to the CIO or is nonexistent. This is in contrast to the corporate world where the trend is to elevate the CISO to a position that is equivalent to the CIO and reporting directly to the CEO.
In a 2008 Governance of Enterprise Security Study conducted by Carnegie Mellon University CyLab, it was found that there is still a gap between information technology (IT) and enterprise risk management. Boards and senior executives are not adequately involved in key areas related to the governance of enterprise security. This reinforces the need for local governments to consider elevating the CISO to a position that is equivalent to the CIO and reporting directly to the City Manager or top elected and/or appointed official. Doing so would bridge the gap between IT and enterprise risk management, and better protect local government systems and data from cyber threats.
This is echoed by the International City/County Management Association (ICMA) LG Cybersecurity Survey 2020, which recommends that local governments consider elevating the CISO to report directly to the top elected and/or appointed official. Doing so would demonstrate the importance of cybersecurity throughout the organization and improve communication between the CISO and top officials in local government.
Separating the security leadership function out of IT has clear governance benefits, but it is not without drawbacks. Gartner's report "Determining whether the CISO should report outside of IT" highlights some of the potential disadvantages of separation. One significant challenge is that conflicts may arise between the CIO and CISO, particularly around issues such as ownership of assets and alignment of IT and cybersecurity work. In some cases, the CISO may also have less influence or authority within IT. Additionally, separating the CISO from the IT function can be less complicated than a matrixed team management approach.
In a structure where a CSO reports to a CIO it can result in "over-leveraging towards cost management as opposed to risk management." - Dave Burg, EY Americas
Despite these challenges, there are several benefits to having separate reporting structures for the CIO and CISO. One significant advantage is greater segregation of duties, which helps prevent conflicts of interest and improves objectivity. Clear lines between first and second lines of defense also make it easier to engage enterprise-wide stakeholders and achieve more mature governance of information and technology. Having executive-level IT and cybersecurity positions ensures consideration of IT and cyber risk at the appropriate level. Finally, having a CISO role would include non-IT security responsibilities, such as Operational Technology (OT), physical security, EOC, Legal, Audit, etc., helps promote a greater understanding within the organization that cybersecurity is not solely an "IT problem."
The role of the CISO is becoming increasingly important as cybersecurity risks continue to rise. However, it's not just the role of the CISO that's important; it's also where the CISO fits within the organization. Reporting relationships are more than just lines on an org chart; they represent lines of authority. Who the CISO reports to can be an indicator of the organization's maturity when it comes to cybersecurity.
As an organization matures, the CISO becomes more aligned with the business. Instead of being completely IT-centric and reporting to the CIO, the CISO should report directly to the CEO or another executive who can provide the necessary authority and visibility for cybersecurity risks. This allows the CISO to become a committee chairman, responsible for gathering and communicating cross-organizational metrics that will be packaged and presented to leadership.
"The CISO becomes a committee chairman, responsible for gathering and communicating cross-organizational metrics that will be packaged and presented to leadership." - Kris Lovejoy, BluVector CEO
To be effective, the CISO needs to break outside of the IT silo and become business-centric. Managing security effectiveness and risk management transcends IT and has to operate at an executive level so that technical and non-technical decision-makers can be armed with evidence-based data in order to make informed business decisions more effectively and efficiently. By separating the CISO function from IT and having the CISO report directly to an executive, the organization can achieve greater segregation of duties, improve objectivity, and ensure clear lines between the first and second lines of defense.
"In this model, security architecture resides in each of the functional areas of the organization, with the CISO providing governance and transparency." - Lamont Orange, Netskope CISO
It's not just the role of the CISO that's important, but also where the CISO fits within the organization. A mature organization will have the CISO reporting directly to an executive outside of IT, allowing the CISO to become business-centric and provide evidence-based data to inform business decisions. Ultimately, the goal is to break outside of the IT silo to ensure that cybersecurity is viewed as an enterprise-wide issue and not just an IT problem.
When it comes to the reporting alignment of a CISO, there is no one-size-fits-all solution. Most executives acknowledged that a CSO reporting to a CIO is still the most common scenario, but also agreed that it was not always ideal. When asked about their preferred reporting alignment, they had many suggestions. Ultimately, the best reporting alignment for a CISO depends on the organization's size, culture, and desired maturity level. I will review some of the org chart possibilities and the maturity levels in another blog post.
Resources
The ICMA LG Cybersecurity Survey 2020
IDG's 2020 Security Priorities Study
Does it matter who the CISO reports to? (MAR 2021) https://www.csoonline.com/article/3278020/does-it-matter-who-the-ciso-reports-to.html
Determining Whether the CISO Should Report Outside IT- Gartner ID G00743363 - (APR 2021)
How the CISO role is evolving (APR 2021) https://www.csoonline.com/article/3332026/what-is-a-ciso-responsibilities-and-requirements-for-this-vital-leadership-role.html
SANS https://www.sans.org/blog/cybersecurity-leadership-triads/
What does a business information security officer do? (AUG 2021) https://resources.infosecinstitute.com/topic/what-does-a-business-information-security-officer-do/
The Rise of the Business-Aligned Security Executive - Forrester (Aug 2020)











































Comments