Navigating AI ChatBots: Establishing Guidelines and Embracing Change
In a recent discussion, the remarkable potential of artificial intelligence (AI) and its associated risks took center stage....


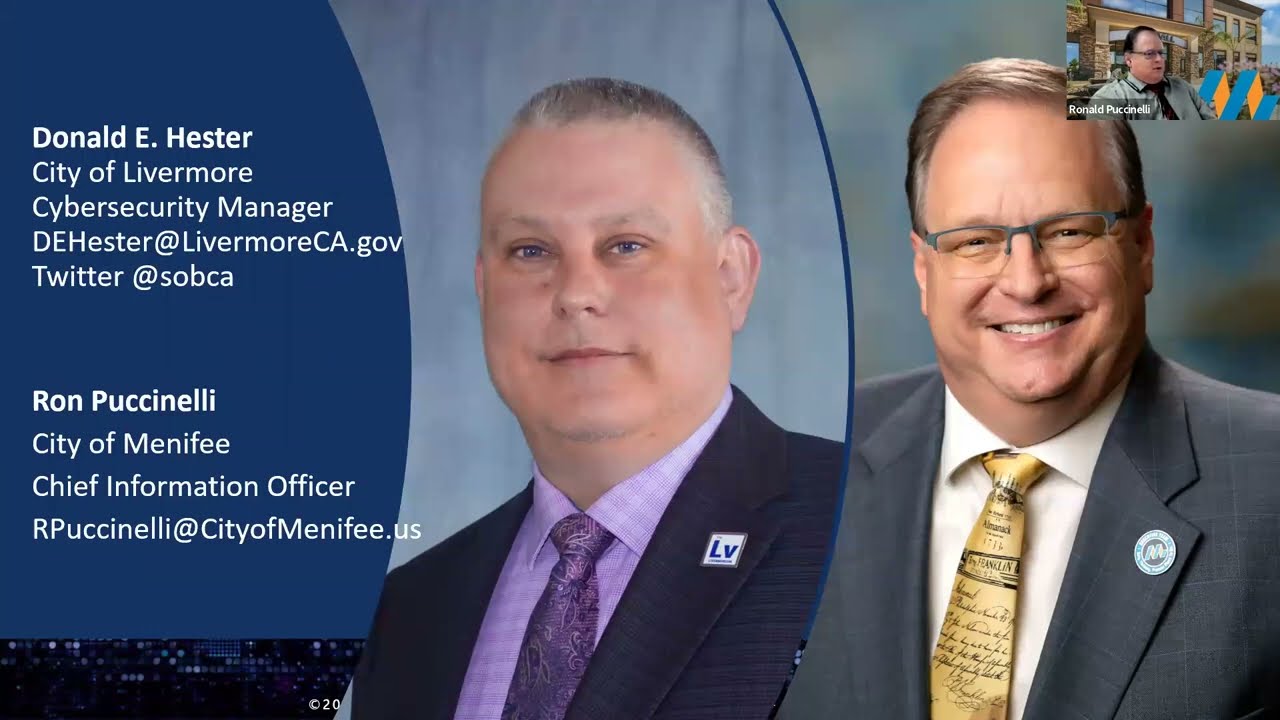
Ensuring Transparency and Disclosure: Navigating Cybersecurity Risks in the Municipal Bond Market
I recently had the honor of being selected to participate in a panel discussion on assessing, mitigating, and disclosing cybersecurity...


Cybersecurity Procedure Coverage
In a previous post, I outlined the required topics for cybersecurity policies. In this post, I will cover the required procedures from...


What Should be in a Good Cybersecurity Policy
I often get called in to evaluate cybersecurity documentation, more specific policies and procedures. One of the concerns is what to...


Policy, Procedure, or Plan
Some standards like PCI and NIST require policies that cover specific topics. Sometimes you will see a requirement for a policy and...


IT Governance & IT Management
Many practitioners use these terms governance and management synonymously. While there is some overlap in practice, there are key...


Cybersecurity Policies Made Easy
People often ask for advice regarding information security or cybersecurity policies. For the remainder of this article, I will use...


Cybersecurity Policy for Local Governments
Here is a sample high-level cybersecurity policy for a city, district, or county. It is designed to be a high-level statement adopted by...


Sample Ethics Policy, Academic
Ethics Project - Create a Sample Ethics Policy - American Military University, Criminal Justice Department Global Bank ABC We[1] the...