The Importance of the CISO
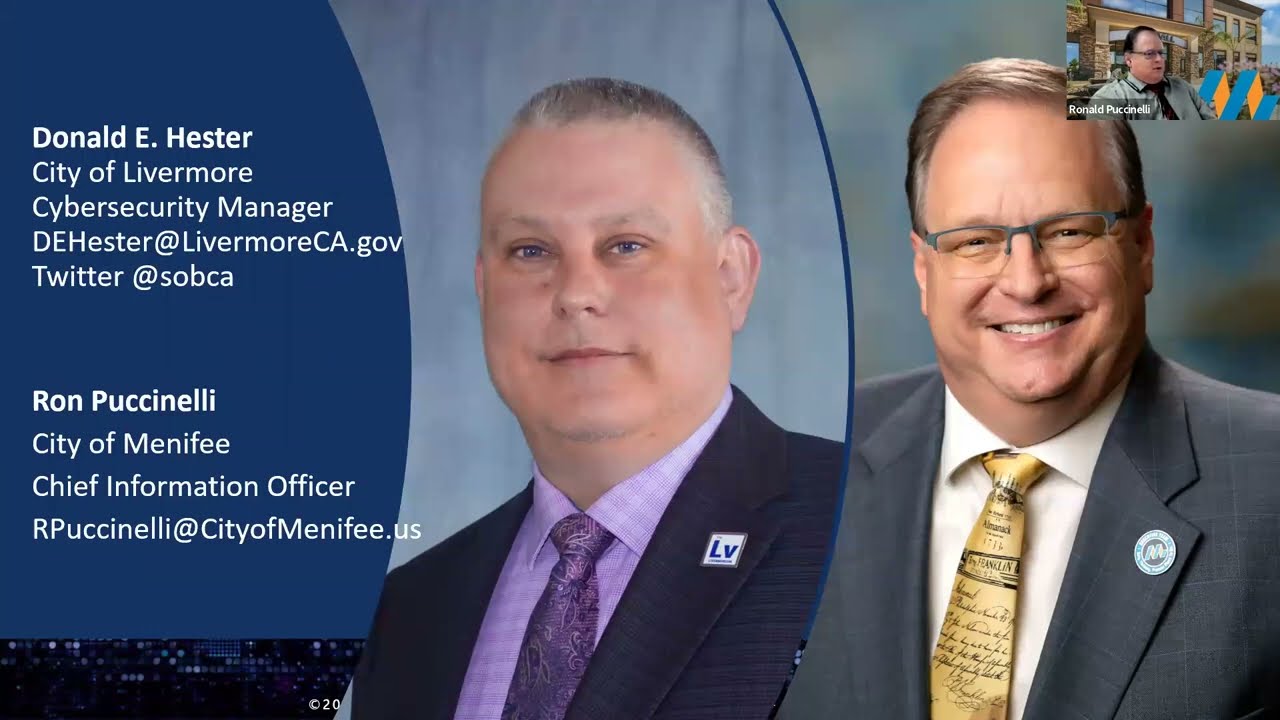
- Donald E Hester
- Feb 5, 2020
- 4 min read
Updated: Feb 16, 2023
A survey by ThreatTrack demonstrates that the role of CISO is misunderstood and underappreciated by C-Level peers. It seems business executives do not have confidence that the CISO understands the business. It seems many executives make business decisions that have cyber risk without input from their CISO. Or the responsibility of cyber risk management and compliance is placed with the head of IT (CIO or director). Often the head of cybersecurity does not have an audience with the business decision-makers because they are too far down the organization hierarchy to be useful or even heard. This increases the disengagement between cybersecurity and the organization. In the end, this tangibly hurts the organization.
Many executives also conflate or confuse the outsourced CISO with an outsourced Security Operation Center (SOC) or SOC-as-a-Service (SOCaaS). They are not the same thing, and I will have to cover that in a future post.
So what is a CISO? A Chief Information Security Officer (CISO) is the senior-level executive within an organization responsible for developing and maintaining the enterprise governance program to ensure information assets and technologies are adequately protected. The CISO directs staff in identifying, developing, implementing, and maintaining processes across the enterprise to reduce business risks related to compliance, information, and information technology. The CISO you choose must be empowered to integrate with the business and become an enabler of business processes.

Many organizations are too small to afford a full-time CISO. However, the business risk to smaller organizations may be even higher than to larger organizations that have a mature governance program. To fill this need many consultants are now offering CISO-as-a-Service (CISOaaS) or Virtual CISO (vCISO) services to provide those smaller organizations the benefits once only available to enterprise size organizations. The services vary from provider to provider; however, they typically include governance, cyber risk, and compliance consulting so that senior management and decision-makers can make business decisions based on the risk to business operations.
The two goals of a mature governance program are to establish policies and procedures to ensure the information and technology bring a benefit to the organization and that the risks associated with the information and technology are appropriately mitigated. It is critical for senior management to understand the benefits and risks related to information and technology in order to make sound business decisions. The CIO’s (head of IT) role is to ensure that technology brings value to the organization and that resources are used efficiently. The role of the CISO (head of cybersecurity) is to ensure that compliance and risks related to information technology are communicated to key stakeholders and senior management so they can make informed decisions.
For many smaller organizations, unfortunately, the responsibilities of the CIO and CISO are placed on the same individual. One risk in placing both sets of duties on one individual is that there is a tendency for people to focus more on what they know, this creates an imbalance between value delivery and risk mitigation for the organization. Often there is a conflict between the benefits and risk management that senior management or decision-makers will be unaware of without a second party providing advice.

Another risk related to placing too much responsibility on one person is effectiveness. Often what organizations find is that one person is responsible for too many processes and simply does not have the bandwidth to manage and improve those areas effectively. Organizations tend to be ineffective across their entire process landscape. Generally, this is caused by unclear process ownership. This prevents the IT department from improving critical processes and ultimately leads to underperformance and dissatisfaction.
Of course, it is crucial to understand the benefits of having a CISO. The main advantage is to create a cybersecurity program that is proactive, flexible, and one that enables business. Whether or not the CISO is in-house or outsourced, organizations will benefit from implementing governance processes brought by the CISO. Research shows that organizations that have CISOs benefit in a number of ways.
Benefits of having a CISO:
Reduce business risks.
A CISO will help to increase the alignment between cybersecurity and business objectives.
Reduce wasted cybersecurity efforts and resources.
Improve cybersecurity efficiency.
Ensure the goals of stakeholders and cyber risk are met.
Reduce resistance and gain more support for cybersecurity initiatives.
Cost savings from reducing cyber incidents and the impact of cyber incidents.
Cost savings from optimizing cybersecurity investments.
Cost savings by ensure alignment with business objectives.
Improved public reputation.
Continuous improvement of business processes.
Ensure technology bring value to the organization and that risks are managed.
Proactive planning for the future.
What to do?
If you don’t have a head of cybersecurity for your organization, get one. Don’t place the responsibility on the head of the IT department. The CIO and CISO will work closely, but the job roles and knowledge-based are vastly different. If you have someone on staff that is the head of cybersecurity, are they in a position within the organization chart to help inform key stakeholders, business decision-makers and executives, of cyber risks? If not, they need to move up.

Of course, an external assessment might help to make a case for a CISO and the proper location within the organization. What is not a good idea is to ignore the importance of someone managing cyber risk for your organization. Remember cyber risk is business risk.












































Comentarios