Spot a Scam
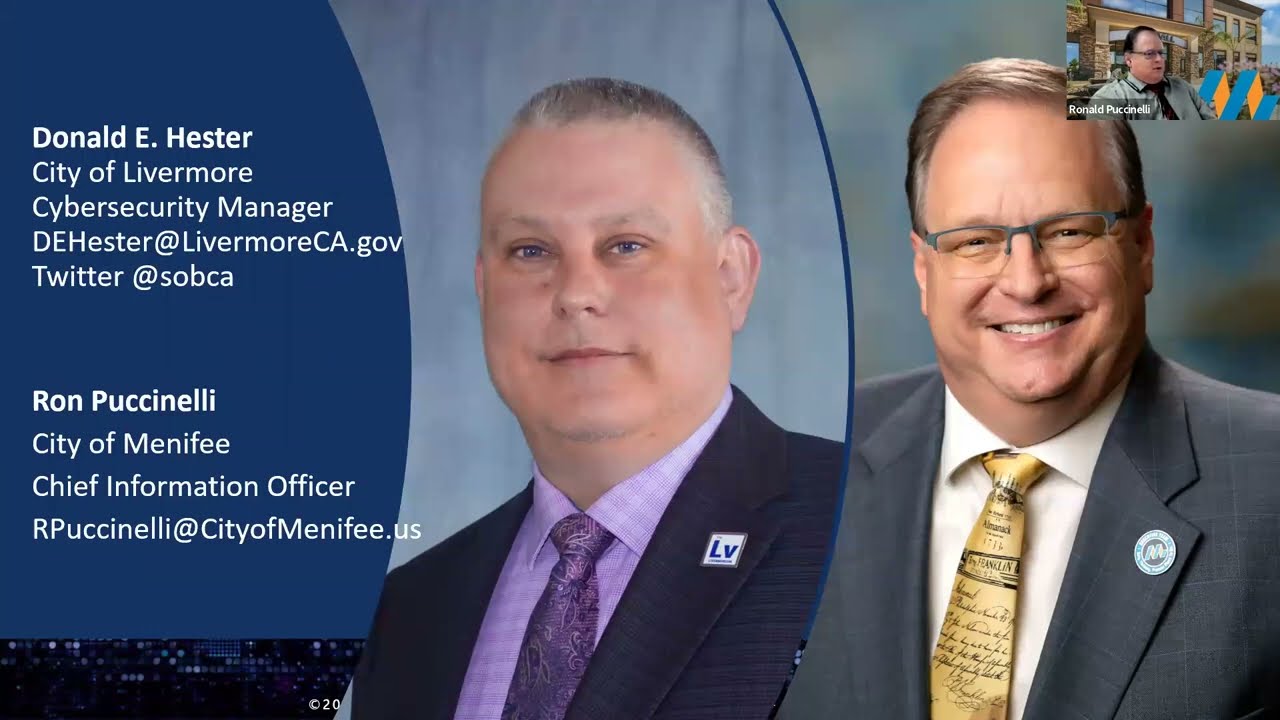
- Donald E Hester
- Mar 9, 2020
- 4 min read
Updated: Feb 16, 2023
In cybersecurity awareness programs, we try to keep people informed of the latest scams. However, it seems like we are chasing a carrot on a stick. Scammers are continually changing up their scams, and it is nearly impossible to keep up with the rapid changes. This leads IT professionals to advise people not to click on links. However, the problem with that advice is the Internet is based on clicking links, and we send users links we want them to click on all the time. Asking people not to click on links and then send them links to click on is confusing and counter-intuitive for users. IT and cybersecurity professionals risk turning we into a meme, “don’t click… do click… don’t click.” Users are understandably frustrated if people have to be able to click on links to do their jobs we need to stop telling them to not click and focus on training them to be wise clickers.

How is it that scammers are able to trick the average person into making costly and humiliating mistakes? How is it that even the smartest people can fall for apparent scams? Simple, scammers have long understood what we call the amygdala hijack. Scammers use tactics to trigger the amygdala to impair the victim’s prefrontal cortex and rationality. Victims go from stimulus directly to response in the often-called fight or flight mode.
How can we make them wise clickers? We want to help users inject rationality between stimulus and response. In order to accomplish that, it takes knowledge, training, and practice. To that end, I want to outline some comment tactics of scammers in hopes that would be victims we see the red flag and respond in a safe fashion.
Phishing Tactic #1: Urgency
Usually, there is an appeal of urgency to get you to act fast without taking the time to think about the scammer's request. A red flag should go up anytime you receive an urgent request and be extra vigilant. For example, a scammer impersonated a City Manager and made a request of staff in finance to send her the W-2 for the previous year. The message said that he was in a meeting and needed them immediately for that meeting.
Phishing Tactic #2: Authority
Scammers will often pose as authority figures in an attempt to make demands on their targets without being questioned. Scammers will impersonate top executives, law enforcement, government officials, or anyone in authority, in order to gain compliance from the victim. As in the local government example above, the City Manager is an authority figure that most employees will seek to impress, try to be the hero, or to help out.
Phishing Tactic #3: Scarcity
Scarcity plays to people’s desire to benefit themselves financially. In pyramid schemes or investment fraud, a scam may be presented as a limited opportunity. In email form, scammers pose as authority figures to get you to click on links or provide passwords and information without paying any close attention to the actual message or its sender. Threatening or aggressive behavior to bully their targets into compliance.
Phishing Tactic #4: Credibility
Scammers will do what they can to make the request look as creditable as possible either by fabricating identities or offering a plausible request. When the request has an aspect of truth, the request gets a little boost of legitimacy. For example, most people shop online today, and it is entirely credible and reasonable to receive a shipping notification. For local governments, a considerable amount of information is easily accessible, such as the winner of a contract. Scammers can use this information to set up wire transfer information for the winner of the contract before the legitimate company does. The request seems credible because it is an expected request.
Phishing Tactic #5: Panic, Fear, Anxiety
Scammers can rely on fear to hijack your brain with good old fear tactics. Fear of punishment, for example, is used by scammers who call pretending to be from the IRS with a past-due bill and the threat of jail time. Other scammers may call claiming to be from a tech company claiming they know you have a virus on your computer asking if they can remote into your computer in order to hijack it. Your fear of having a computer virus or losing all your family photos hijacks your brain.
Phishing Tactic #6: Strong Emotions, Empathy or Anger
Some scammers will appeal to your sense of compassion to get you to react. One example of a scam is a request to donate to well-publicized disasters. Donation requests from fake organizations often follow disasters, like the fire of Notre Dame. Another example may ask you to click a link and join a cause for justice that plays on your anger over the injustice.
Phishing Tactic #7: The Combo
Scams can use more than one tactic in a single attempt. For example, scammers claiming to be from the IRS appeals both to authority and our sense of fear.
Another thing to help avoid being a victim is to know what scammers are typically after. What do scammers try to get you to do? Scammers are trying to get you to do something, almost always, there is some form of a request from the scammers. The requests often are asking you to do something, like click on a link, download a file, or they may even request confidential information like a password. Of course, there will be requests that are legitimate that are not from scammers. For example, a business partner may want to share a file with you. To be a wise clicker, you may want to confirm with the sender that they did, in fact, send you a file.
Examples of requests to treat with extra caution:
Click a link
Open a file
Download a file
Disclose information
Disclose password
Transfer funds (Wire transfers, gift cards, direct depots, donations, bail money, etc.)
How do scammers contact you? Most scams originate via email, however, text messaging and voice phone calls are also on the rise. Scammers will use any means at their disposal, so we have to be vigilant no matter how we receive a request.
I hope these tips or little tidbits of knowledge will help equip you in spotting a scam.












































Comments