Most Popular Cyber Scams
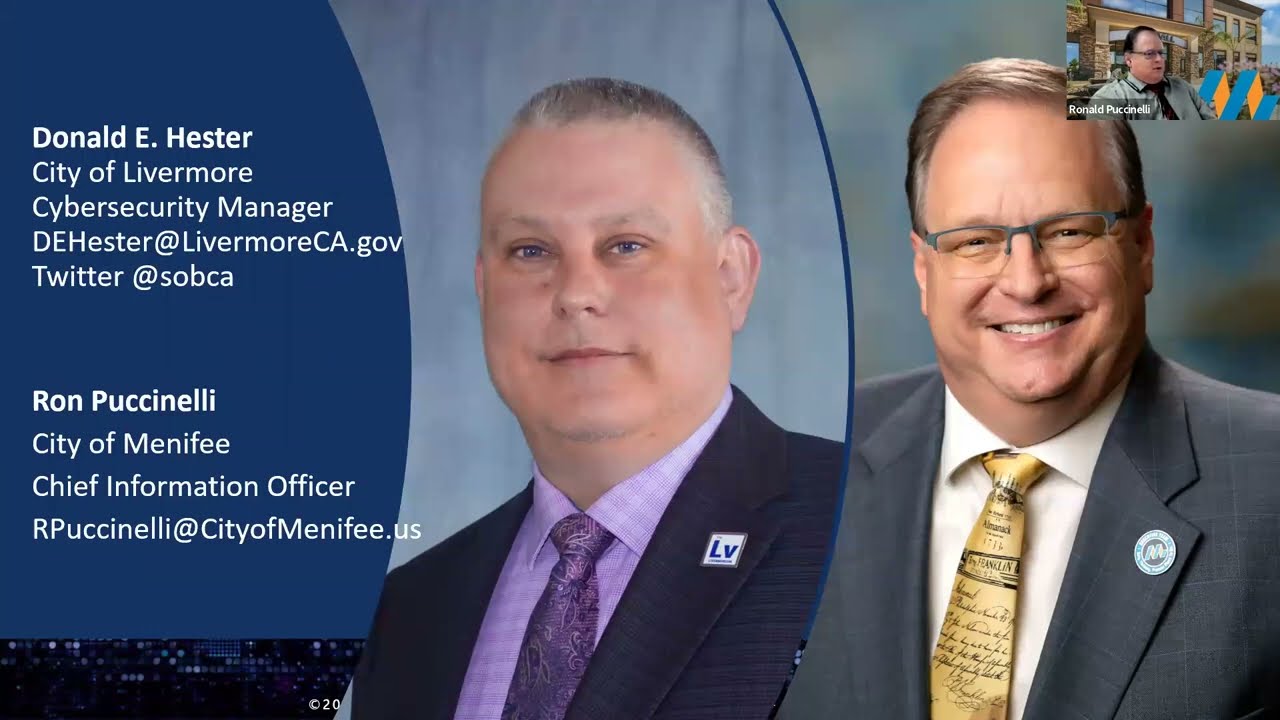
- Donald E. Hester

- Aug 2, 2018
- 5 min read
Updated: Apr 1, 2023
Cyber scams and online fraud continue to evolve. Law enforcement and cybersecurity professionals try to prevent online fraud by educating people on the typical methods used by cybercriminals and fraudsters. Criminals respond necessarily by continuously changing their tactics in order to continue to defraud victims. Much like the arms race, each side escalates to get ahead of the other.

It may seem defeatist or pessimistic, but it is not. It simply means we must remain vigilant. We cannot throw our arms up in pessimism and surrender. We must continue to educate people on the general types of scams, how to spot them and insulate themselves from them.
On the lighter side, you can find multiple scammer phone calls recorded on YouTube. Some of them are downright funny. Most of the time it is people who know it is a scam and they play with the scammers. The nice thing about their service is they waste scammer’s time giving the scammers less opportunity to scam others. Another benefit to them recording and posting the calls is it gives others the ability to be entertained and educated at the same time.
Here is an earlier blog post on this
Defining terms and explaining popular cyber scams
Social Engineering
Social engineering is the psychological technique of manipulation used by criminals to trick people into doing something that will leave the person or an organization exposed. Criminals can trick people into disclosing information, granting them access to systems or locations, performing actions that will violate organizational policies or clicking a link to download malicious software.
One thing to remember is as people become aware of scams the con artists respond by changing their tactics.
Phishing
Phishing is a type of social engineering attack where cybercriminals will send mass emails out, masquerading as a trustworthy entity, as bait in hopes to get someone to respond, divulge information or click a link that can download malicious software. Often this is used by cybercriminals to acquire sensitive or personal information such as usernames, passwords, and credit card information or it may be a part of a larger scam.
Spear Phishing
Spear phishing is a subtype of phishing where the perpetrator gathers information about the target and uses that information to target an organization or individual. With phishing there is typically a shotgun approach using genetic information such as sending an extensive list of recipients a spoofed email from Bank X. Many of the recipients would not be fooled because they don’t have an account at Bank X. With spear phishing information gathered is used to target the recipient. For example, a cybercriminal discovers an individual is a client of an Insurance Company A and uses that information to send an email pretending to be from Insurance Company A. The recipients are more likely to take action if they think it is from an institution or individual they already have a relationship with.
Business E-Mail Compromise
Business email compromise is a type of spear phishing attack where a cybercriminal impersonates a high-ranking executive, like CEO, and attempts to get an employee, partner, or vendor, to disclose sensitive or confidential information, trade secrets, or make a wire transfer. Cybercriminals have targeted payroll or human resources personnel to disclose employee information such as W-2s. They have also targeted accounts payable to make a wire transfer to an offshore account.
This attack method attempts to exploit people’s desire to be helpful, their compliance to authority, and the pressure of urgency. The attacker almost always creates a sense of urgency so that people will not take time to think.
Tech Support Scams
Another scam cybercriminals will attempt is to impersonate a representative for a software company and contact you by phone, email, or pop up notification, and claiming they are there to help with a virus or someone other issue like licensing of your software.
This method of attack exploits people’s fears of getting a virus. Again, urgency is used to get people to give access to their computers for fear the virus will spread.
IRS or Tax Scam
In this scam, the cybercriminal will impersonate and ISR agent in an attempt to get the victim to pay an outstanding tax liability. The scam is often a phone call but can also come via email.
This attack method attempts to exploit people’s fear of criminal prosecution and compliance to an authority like the IRS.
Advance Fee Fraud
Advanced fee fraud is one of the oldest cons dating back to medieval times. The con starts with a promise of large sums of money, land, or interest in some venture. As the scam progresses there will be a request for upfront money or fee to release the larger sum of money. Some of these con artists bait the victim and carry out the scam over a number of weeks or months.
One common example of the advanced fee fraud is called Nigerian fraud. The scam is someone impersonating a Nigerian government official who is offering a portion of the money he or she is trying to get out of the country. This version of advanced fee fraud will attempt to have the victim prefund a foreign bank account, for verification purposes, before the larger sum of money can be deposited. Once the advance was made it is withdrawn by the fraudster. Often identity theft is included with the advance fee fraud. In some incidents victim have been lured to Nigeria to collect money and are asked to bring more money with them. Those victims end up being robbed and possibly murdered.
This attack method attempts to exploit people’s greed. People will often respond to a get rich scam.
Debt Elimination Fraud
Debt elimination scams basically promise they will help you eliminate your debt, often claiming legal methods of debt relief. The scammer requires a fee or membership in order to proceed. Victims often end up with damaged credit rating and lawsuits.
This attack method attempts to exploit people’s greed. Specifically, not having to pay what they owe.
Charity Fraud
Charity fraud is where an imposter poses as a non-profit seeking to do some good in the world. The scam attempts to get people to donate to their cause. Typically, they ask for credit card payments, western union payments or gift cards.
These scams vary widely from disaster relief, which typically peaks for just about every disaster, to veterans in need of help. Often pleas for help are posted on crowdfunding sites or social media sites. Some even request direct support of an individual in a foreign country that is not eligible for some technical reason for support from legitimate charities.
This attack method attempts to exploit people’s charitable nature or desire to be helpful. Guilt for not providing help may also be used by the scammers to convince you to “give.” This type of fraud will also peak during the holiday season because people may be more charitable and possibly seeking more tax deductions.
Identify Theft
Identity theft is where the con artist pretends to be you. Identity theft is not a form of social engineering, but it is a common result of social engineering or the result of a data breach. Identify theft is the use of your personal information by a fraudster to gain a financial advantage, obtain credit or get other benefits. The imposter typically assumes a person's name or identity to make transactions or purchases. This leaves the victim with bills or bad credit.
Final Thoughts
This is not an exhaustive list of the types of cybercrimes. I can’t go over all the types, but I can go over some of the most common scams out there. As stated before criminals continue to evolve their schemes requiring constant vigilance from law enforcement and cybersecurity professionals.
Resources












































Comentarios