Three Cybersecurity Bad Practices You Should Avoid to Protect Your Organization
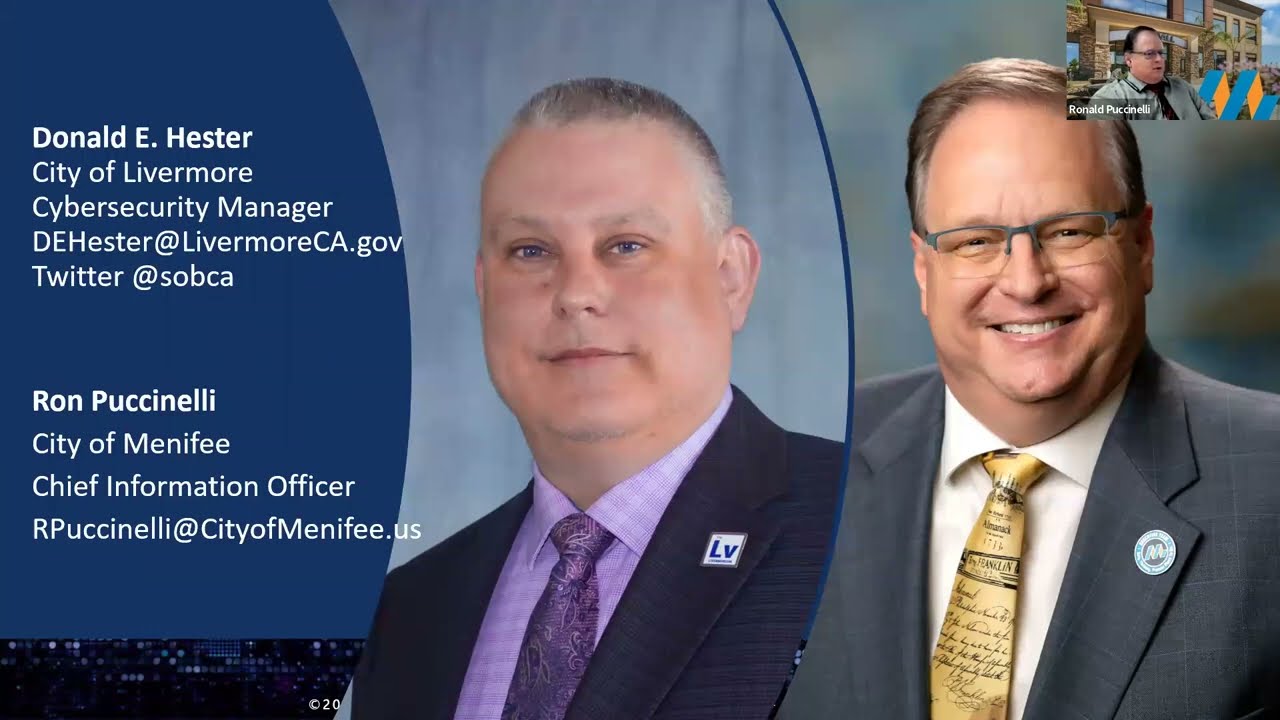
- Donald E. Hester

- Mar 6, 2021
- 2 min read
What Not To Do: The CISA's Bad Practices
In today's digital age, cybersecurity is critical to the smooth functioning of organizations, especially those supporting Critical Infrastructure or National Critical Functions (NCF). The cybersecurity risks faced by these organizations can impact national security, economic stability, and public health and safety. To address these risks, the Cybersecurity and Infrastructure Security Agency (CISA) has developed a catalog of Bad Practices that should be avoided to ensure cyber safety.

1.
The catalog includes practices that are exceptionally risky, especially in organizations supporting Critical Infrastructure or NCFs. The first bad practice listed is the use of unsupported software. This practice is dangerous and significantly elevates the risk to national security, economic security, and public health and safety, especially in technologies accessible from the Internet. Unsupported software is no longer receiving updates or security patches, which leaves it vulnerable to cyberattacks.
2.
The second bad practice listed is the use of known/fixed/default passwords and credentials. Using these types of passwords and credentials increases the risk of cyberattacks and compromises the security of your organization. Cybercriminals can easily exploit these weak passwords and gain unauthorized access to sensitive information or systems.
3.
The third bad practice listed is the use of single-factor authentication for remote or administrative access to systems supporting your organization. Single-factor authentication, such as a password, is no longer sufficient to protect sensitive data or critical systems. It is essential to use multi-factor authentication, which requires users to provide additional credentials, such as a security token or biometric authentication, to ensure a higher level of security.
CISA encourages all organizations, not just those supporting Critical Infrastructure or NCFs, to engage in the necessary actions and critical conversations to address Bad Practices. While the list is not exhaustive, it provides a good starting point for organizations to evaluate their cybersecurity practices and ensure they are taking the necessary steps to mitigate risks.
It is important to note that avoiding these three bad practices alone will not make an organization fully secure against cyber threats. However, they are critical steps towards building cyber resilience. Cybersecurity is a continuous process, and organizations must remain vigilant and proactive in implementing robust cybersecurity measures to mitigate risks effectively. Avoiding these bad practices is just one piece of the puzzle, and it must be accompanied by other cybersecurity practices, such as regular software updates, employee cybersecurity awareness training, and the use of advanced cybersecurity tools and technologies. By adopting a comprehensive and proactive approach to cybersecurity, organizations can significantly enhance their cyber resilience and protect themselves against cyber threats.
In conclusion, the CISA Bad Practices catalog serves as a wake-up call for organizations to take their cybersecurity seriously. To protect your organization, critical infrastructure, national security, and public health and safety, it is essential to avoid these bad practices and adopt robust cybersecurity measures. By working together and sharing best practices, we can mitigate cybersecurity risks and ensure a safer and more secure digital world.









































Comments