New Roles in Local Government Cybersecurity: A Guide to the CISO, BISO, CPO, and CSO
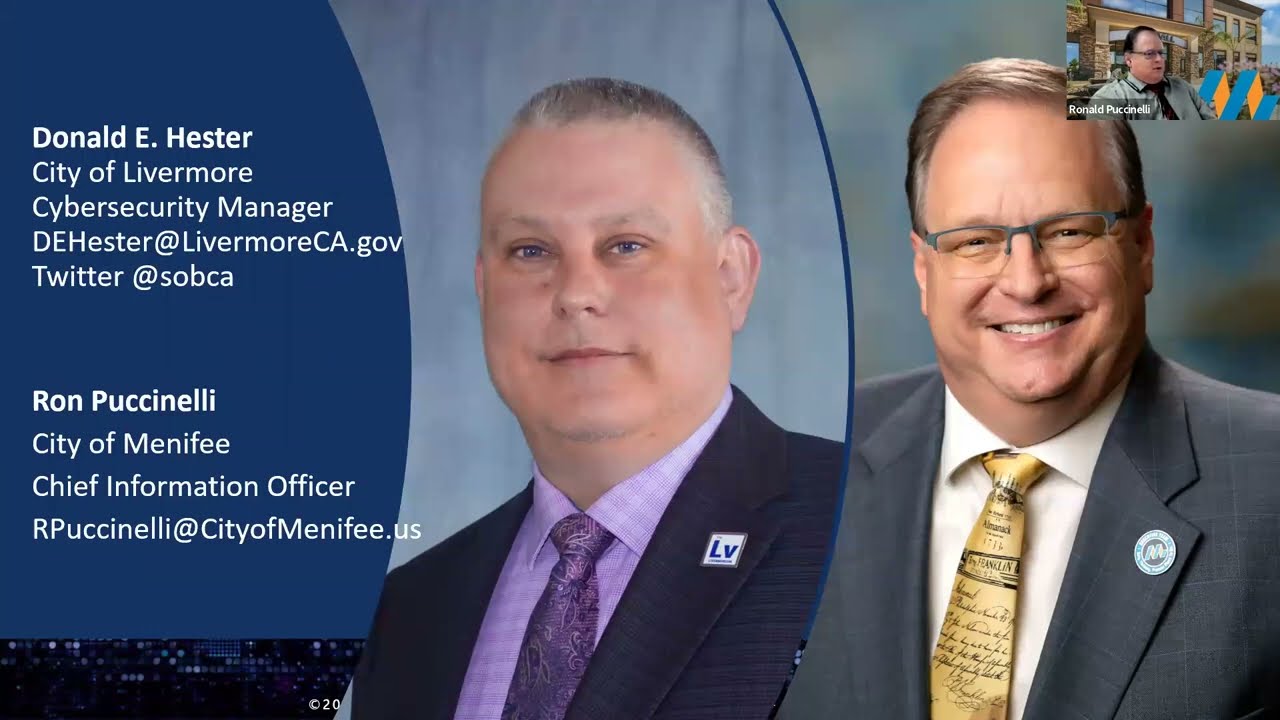
- Donald E. Hester

- Jan 29, 2022
- 7 min read
The rapidly changing cybersecurity landscape has forced local governments to reevaluate their approach to cybersecurity. With the increasing sophistication of cyber threats and the need to protect sensitive information and critical infrastructure, new roles are emerging to assist councils and boards in addressing cybersecurity challenges. The traditional roles of IT managers and network administrators are no longer sufficient to meet the demands of modern cybersecurity. Instead, new roles such as Chief Information Security Officer (CISO), Business Information Security Officer (BISO), and Cybersecurity Analysts have become essential in ensuring the protection of sensitive information and critical infrastructure. In this blog post, we will explore these new roles and their responsibilities in assisting councils and boards with cybersecurity.

In this post, I will build on my previous post: Finding the Right Fit: Exploring Local Government Cybersecurity Reporting Structures
CISO, BISO, CPO, CSO, CRO, Oh my! What's with all the titles?
Chief Information Security Officer (CISO)
In recent years, the importance of cybersecurity has become increasingly apparent to organizations across all industries. As a result, there has been a growing need for new roles that assist council/boards with cybersecurity. One of the most important of these roles is the Chief Information Security Officer (CISO).
The CISO is responsible for overseeing an organization’s information and data security, as well as the protection of its infrastructure and assets from malicious actors. This is a critical role, as cybersecurity threats are constantly evolving and becoming more sophisticated. The CISO must have the technical expertise and experience needed to stay ahead of these threats and ensure that the organization’s data and assets are protected.
One of the key responsibilities of the CISO is to work with all business units to identify potential risks and develop risk management processes. This involves analyzing the organization’s existing IT infrastructure and identifying potential vulnerabilities that could be exploited by cybercriminals. The CISO must also work closely with other executives to develop a comprehensive business development plan that incorporates cybersecurity considerations into every aspect of the organization’s operations.
In addition to identifying and mitigating risks, the CISO is also responsible for ensuring that the organization’s IT systems comply with relevant regulations and standards. This requires a deep understanding of the regulatory landscape and the ability to keep up-to-date with new regulations as they are introduced.
Another key responsibility of the CISO is to plan, design, and implement an IT and network strategy for the organization. This involves staying up-to-date with emerging technologies and evaluating their potential impact on the organization’s cybersecurity posture. The CISO must also work closely with other executives to ensure that the organization’s IT and network infrastructure is aligned with its overall strategic goals and objectives.
Overall, the role of the CISO is critical to the success of any organization in today’s digital landscape. By working closely with other executives and business units, the CISO can help ensure that the organization is well-protected against cybersecurity threats and that its IT and network infrastructure is aligned with its strategic goals and objectives.
Business Information Security Officer (BISO)

The role of the Business Information Security Officer (BISO) has become increasingly important in recent years as organizations look for ways to bridge the gap between cybersecurity and larger business interests. While the Chief Information Security Officer (CISO) is responsible for overseeing an organization's overall cybersecurity strategy, the BISO serves as a deputy to the CISO and is responsible for implementing that strategy at a more granular level.
One of the main reasons for the emergence of the BISO role is that many organizations are not aware of the various cybersecurity functions that exist, or which functions should be in IT and which should not. As a result, the CISO often focuses on operational cybersecurity functions rather than the strategic, business-centric functions of cybersecurity.
The BISO is tasked with developing and maintaining the security posture of the organization, and works closely with executive leadership to establish and maintain a risk management program. In addition to implementing the CISO's strategy, the BISO is responsible for ensuring that security and business interests are aligned, and that cybersecurity is integrated into the organization's larger business strategy.
By having a BISO, organizations can ensure that cybersecurity is viewed as an integral part of their overall business strategy, rather than simply an operational function. The BISO can help to identify and mitigate risk, as well as ensure that the organization is compliant with relevant regulations and standards. In short, the BISO is a critical component of any organization's cybersecurity program, helping to ensure that security and business interests are aligned, and that the organization is able to operate securely and efficiently.
Chief Privacy Officer (CPO)
As data privacy laws and regulations continue to evolve, the role of the Chief Privacy Officer (CPO) has become increasingly important in local government. The CPO is responsible for ensuring that the collection, use, and storage of data comply with regulatory requirements and internal policies. This role requires expertise in both data privacy laws and organizational policies, as the CPO must develop and implement privacy policies and procedures to ensure that employees are trained and aware of their responsibilities. The CPO also collaborates with other executives to ensure that privacy considerations are incorporated into business decisions, reducing the risk of potential privacy violations. In addition, the CPO monitors compliance with privacy laws and regulations and responds to privacy-related complaints and inquiries. As the amount of data collected by local government increases, the role of the CPO has become increasingly critical to protecting the privacy of citizens and ensuring that the government operates in a transparent and ethical manner. Typically this role is only found in large Cities, Counties or State agencies.
Chief Security Officer (CSO)
The Chief Security Officer (CSO) is a title that was commonly used in the past to refer to the executive in charge of an organization's security. However, with the evolution of cybersecurity and the increased importance of information security, the CSO role has evolved as well. In many organizations, the responsibilities of physical security and information security have merged into one organization. As a result, the CSO role has become more synonymous with the Chief Information Security Officer (CISO) role. However, some organizations still use the CSO title and may include physical security responsibilities in addition to information security responsibilities. Overall, the CSO role is still an important one in ensuring the security of an organization's assets and infrastructure, whether it includes physical or digital security responsibilities or both.
Chief Risk Officer (CRO)
The role of the Chief Risk Officer (CRO) is critical in identifying and mitigating potential threats to the financial and operational stability of a company. In addition to identifying credit, investment, and portfolio risks, the CRO also oversees the identification of potential risks to operational efficiency, personnel liabilities, property inefficiencies, and safety risks. Furthermore, the CRO plays a key role in protecting a company's reputation by recognizing potential threats to the company's brand and image, such as marketing missteps. While the CRO's primary focus is on enterprise risk management, some CROs also oversee cyber risk management as part of their overall responsibility for total enterprise risk management. By identifying and mitigating these risks, the CRO helps ensure the company's long-term viability and profitability.

City Auditor
The City Auditor plays a crucial role in ensuring that the City's operations are efficient, effective, and in compliance with relevant regulations and policies. While the City Auditor's primary responsibility is not cybersecurity, having a dedicated cybersecurity function within the office can greatly enhance the overall security posture of the City. By providing independent oversight and assurance, the City Auditor's office can help identify potential gaps in cybersecurity policies and practices and recommend improvements. Additionally, the City Auditor's office can ensure that cybersecurity risks are properly accounted for in the City's overall risk management framework. Overall, having a cybersecurity function within the City Auditor's office can help ensure that the City's operations are not only efficient and effective but also secure and resilient.
It is worth mentioning that SANS has two different types of cybersecurity leaders that I think align with the separation of cybersecurity functions I wrote about in a previous blog. Why Cybersecurity Needs to be Separated from IT in Local Governments. These are not job descriptions rather, I think they are an attempt to codify the focus on different functions within cybersecurity by separate roles.
Transformational Cybersecurity Leaders
"With enterprises in need of protecting against an endless and increasing onslaught of information security threats, technology management skills alone are no longer sufficient. Today it is about technology, business strategy, and people. Cybersecurity leaders need to be up to speed on information security issues from a technical standpoint, understand how to implement security planning into the broader business objectives, and be able to build a longer lasting security and risk-based culture. Adjusting employees’ and leadership’s way of thinking about security in order to prioritize and act to prevent today’s most common cybersecurity attacks requires organizational change that affects the foundational culture of the organization." - SANS
Operational Cybersecurity Executive
"As cyber-attacks become more common and more expensive, many organizations are making a foundational shift to view operations from the point of view of an adversary in order to protect their most sensitive information. Despite vulnerability tools and programs being available for several decades, breaches still happen regularly from known vulnerabilities. Complicating the matter more are a wide range of modern technologies requiring more time and knowledge to manage, more known vulnerabilities than ever before, an unprecedented migration to cloud, and ever-increasing legal and regulatory compliance standards. Information Assurance Engineers, Auditors, SOC Analysts, and Cybersecurity Managers need more to better defend an organization’s data systems. The SANS Operational Cybersecurity Executive triad is here to help you build, grow, and sharpen your cyber defense team." - SANS
Updated 10 MAR 2023
Resources
The ICMA LG Cybersecurity Survey 2020
IDG's 2020 Security Priorities Study
Does it matter who the CISO reports to? (MAR 2021)
Determining Whether the CISO Should Report Outside IT- Gartner ID G00743363 - (APR 2021)
How the CISO role is evolving (APR 2021)
SANS https://www.sans.org/blog/cybersecurity-leadership-triads/
What does a business information security officer do? (AUG 2021)
The Rise of the Business-Aligned Security Executive - Forrester (Aug 2020)












































Comentários