Locking Down Cybersecurity: Unmasking the Power of Phishing-Resistant MFA
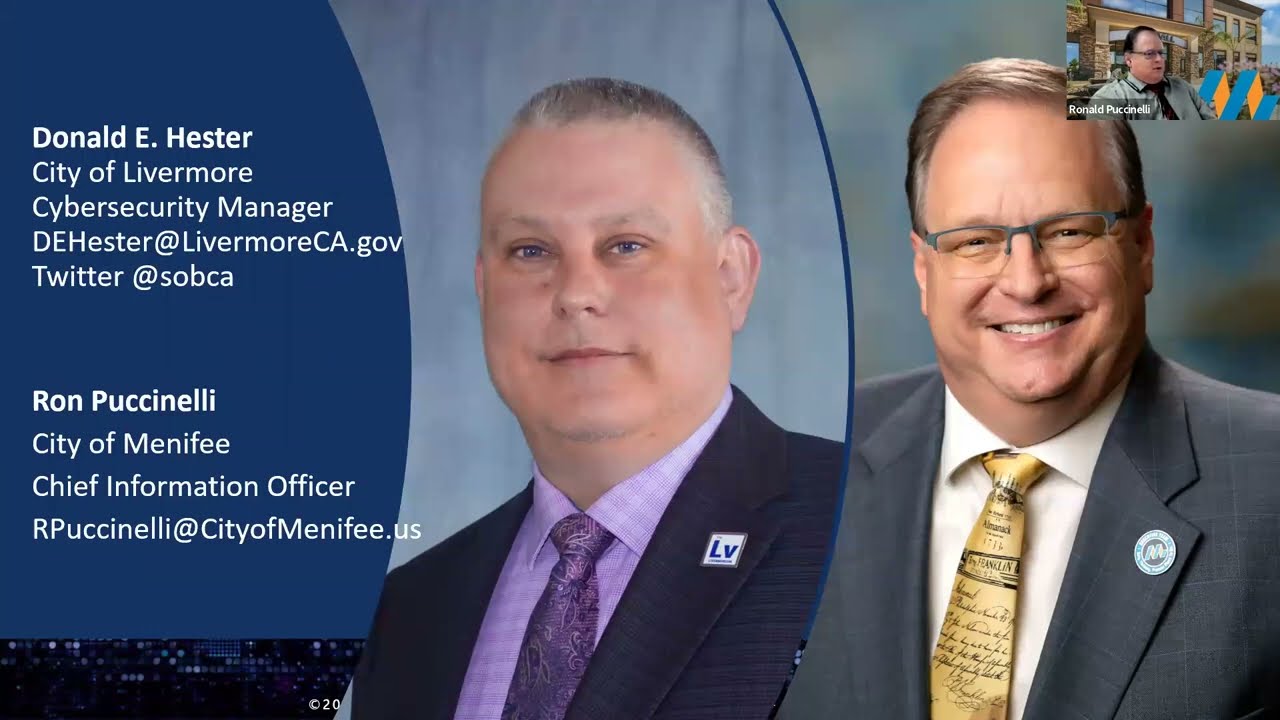
- Donald E. Hester

- Aug 18, 2023
- 6 min read
👋 Just a quick heads-up before you dive into the exciting world of Phishing-Resistant MFA – I'm giving the ol' blog a bit of a makeover. You see, I've decided to ditch the stiff, suit-and-tie vibe for a more chill and casual tone. So, buckle up and let me know what you think of this new style!

Hey there, cyber-savvy readers! I've got a tale to tell that started with a ring of my phone – a call from an organization seeking advice on a topic that's near and dear to my cybersecurity heart. You see, I absolutely relish these conversations because they don't just help out those in need; they also spark the lightbulbs in my brain for new and exciting blog posts!
So, what was the question this time, you ask? Brace yourselves: it's all about the puzzling world of password management. Now, if you've ever ventured into the realm of online security, you probably know how much of a sticky wicket passwords can be. But here's the kicker – the information out there is as diverse as a box of chocolates, and it's enough to make your head spin faster than a hamster wheel.
Picture this: conflicting advice galore, a never-ending tug-of-war between long, complex passwords and short, memorable ones, uppercase vs. lowercase, numbers dancing with special characters... the list goes on! But fear not, my friends, because amidst this chaotic password pandemonium, there's a glimmer of reason that I'd like to shed some light on.
Hold on to your virtual hats, because the first gem of advice I'm going to drop might just blow your mind: it's time to bid a not-so-fond farewell to the age-old password management hustle. Yep, you heard me right. While passwords have been the knights guarding our online kingdoms for ages, it's time to knight a new champion into the cybersecurity realm: MFA, or Multifactor Authentication. But oh, not just any MFA – we're talking about the one that's as cunning as a fox against the craftiest of cyber-tricksters. The one that can thwart the sneakiest of phishing attempts with its impeccable armor – the Phishing-Resistant Multifactor Authentication (MFA).
So, dear readers, buckle up as we dive into the nitty-gritty of why it's time to usher in the era of MFA and bid adieu to the password perplexities. It's time to navigate the sea of contradictory advice and steer our ship towards the shores of cybersecurity clarity. Are you ready to take the plunge? Let's embark on this journey together and unveil the secrets that will help us safeguard our digital lives like never before!
Unmasking the Armor: How Phishing-Resistant MFA Shields Your Digital Realm
In the treacherous landscape of cybersecurity, understanding the battleground is essential. You wouldn't march into a war without knowing your enemy's tactics, right? That's where MITRE ATT&CK® comes into play. This invaluable tool unveils the playbook that threat actors might use, giving us a glimpse of their attack vectors.
Now, let's talk about a knight in shining armor that comes to the rescue of your digital realm – the Phishing-Resistant Multifactor Authentication (MFA). But what exactly does it defend against? Buckle up as we dissect the attack vectors it valiantly addresses, along with the critical layers of protection it provides.
Guarding Against the Shadows: TTPs and Risks Addressed
Brute Force (T1110): Picture a relentless attacker repeatedly striking your gates, trying every possible combination to breach your defenses. Phishing-Resistant MFA thwarts this by adding a layer of authentication beyond the reach of brute force attacks.
Remote Services - Remote Desktop Protocol (T1021.001): The gateway to your digital kingdom can also be a vulnerability. But with Phishing-Resistant MFA, unauthorized access through Remote Desktop Protocol is like trying to unlock a door without the right key – it simply won't work.
Remote Services - SSH (T1021.004): SSH, often used by administrators for remote access, can be a tempting target for attackers. Phishing-Resistant MFA ensures that even if they steal the keys, they can't get past the fortress without a second layer of authentication.
Valid Accounts (T1078, ICS T0859): Compromised credentials are the backdoor to your kingdom. Phishing-Resistant MFA acts as the guardian of these accounts, denying access even to those wielding stolen keys.
External Remote Services (ICS T0822): Protecting external remote services is like safeguarding the outpost of your digital empire. Phishing-Resistant MFA ensures that only the rightful user gets past the gates.
Where the Shield Shines: Scope of Application
The Phishing-Resistant MFA isn't just another weapon in the cybersecurity arsenal – it's the sentinel that watches over IT and OT assets with remote access. Imagine workstations as watchtowers and human-machine interfaces (HMIs) as the command center of your fortress. Wherever safe and technically capable, this armor finds its place.
The Battle Plan: Recommended Actions
The battle plan is simple, yet profound: Fortify your defenses with MFA. Here's how:
For IT:
All IT accounts become invincible with MFA. Priority goes to the high-risk accounts, the privileged administrative gatekeepers of key IT systems. With Phishing-Resistant MFA, these guardians stand strong against any onslaught.
For OT:
Within the OT realm, MFA is the rule for accounts and systems accessed remotely. Be it vendor or maintenance accounts, user workstations, engineering stations, or the vigilant HMIs – all must pass the Phishing-Resistant MFA checkpoint.
The Layers of Invincibility: MFA Options
Hardware-based, phishing-resistant MFA: Think of it as the impenetrable armor that shields your identity. FIDO/WebAuthn or public key infrastructure (PKI) based options ensure that even the craftiest phishing attempts are futile.
Mobile app-based soft tokens: These are your battle-tested companions. Preferably with push notifications and number matching, these tokens are poised to defy any virtual assault.
Emerging technology: FIDO passkeys are the future's keys to security. These rapidly evolving technologies add an extra layer of defense to your digital fortress.
SMS or voice: As a last resort, when all else fails, these options offer a sliver of protection. While not the most impervious, they still stand firm against some threats.
A Fortress Built to Last
In the ever-evolving cyber landscape, Phishing-Resistant MFA is the cornerstone of your fortress's defense. It stands as an unyielding barrier against the relentless onslaught of attackers. From the labyrinth of password pitfalls to the shadowy realms of remote access risks, this guardian is there to ensure your digital realm remains safe, secure, and impenetrable. So, join the ranks of the MFA defenders and let's safeguard our kingdoms together.

A Shield, Not a Bubble: Embracing the Limits of Phishing-Resistant MFA
As we draw the curtains on our exploration of Phishing-Resistant Multifactor Authentication (MFA), it's time to acknowledge the incredible strides this armor has taken in the realm of cybersecurity. We've uncovered its prowess in thwarting attack vectors like brute force attempts, remote access exploits, and compromised credentials – all with the intention of creating a more fortified digital landscape.
Yet, let's not get lost in the allure of invincibility. While Phishing-Resistant MFA stands as a stalwart guardian, it's crucial to remember that no silver bullet exists in the world of cybersecurity. Just as ancient castles with their high walls and deep moats were not impervious to all threats, even the most sophisticated defenses can't eliminate risk entirely.
We must come to terms with the reality that, despite our best efforts, adversaries will always seek new ways to infiltrate and disrupt. No matter how robust our measures are, a determined attacker can still find a chink in the armor. Cybersecurity is a perpetual battle, and while Phishing-Resistant MFA is a powerful weapon in our arsenal, it's not an impervious barrier.
So, as we stand on the brink of fortified security, let's keep our expectations realistic. The goal of Phishing-Resistant MFA isn't to create an impenetrable bubble, but to reduce the attack surface and make breaching our defenses substantially harder. We must remain vigilant, continuously adapting to emerging threats, and layering our defenses to cover every possible angle of attack.
In the end, while Phishing-Resistant MFA indeed goes a long way in reducing cyber risk, it's a single tile in the larger mosaic of cybersecurity. No control, no matter how advanced, can guarantee absolute safety. What we can guarantee, however, is our commitment to the ongoing fight for digital security. As long as we keep our shields up, our strategies sharp, and our adaptability high, we'll stand a fighting chance against the ever-evolving realm of cyber threats.
Notes
About those snazzy images you're seeing? I put on my creative hat and used the Image Creator powered by DALL·E, a nifty tool from Microsoft Bing, to whip 'em up. Gotta admit, they're not too shabby, but here's the scoop: even the coolest AI sometimes has its quirks. Faces seemed to throw it for a loop, resulting in some interesting (read: wild) options. We're talking avant-garde art, folks! 😄
But hey, let's cut AI some slack – it's a work in progress, just like the rest of us. As we ride the AI wave into the future, glitches and all, let's keep in mind that every pixel of progress is a step closer to perfection. So, enjoy the blog and remember, it's all about the journey, quirks and all! 🌟









































留言