Hacks, Time to Discovery
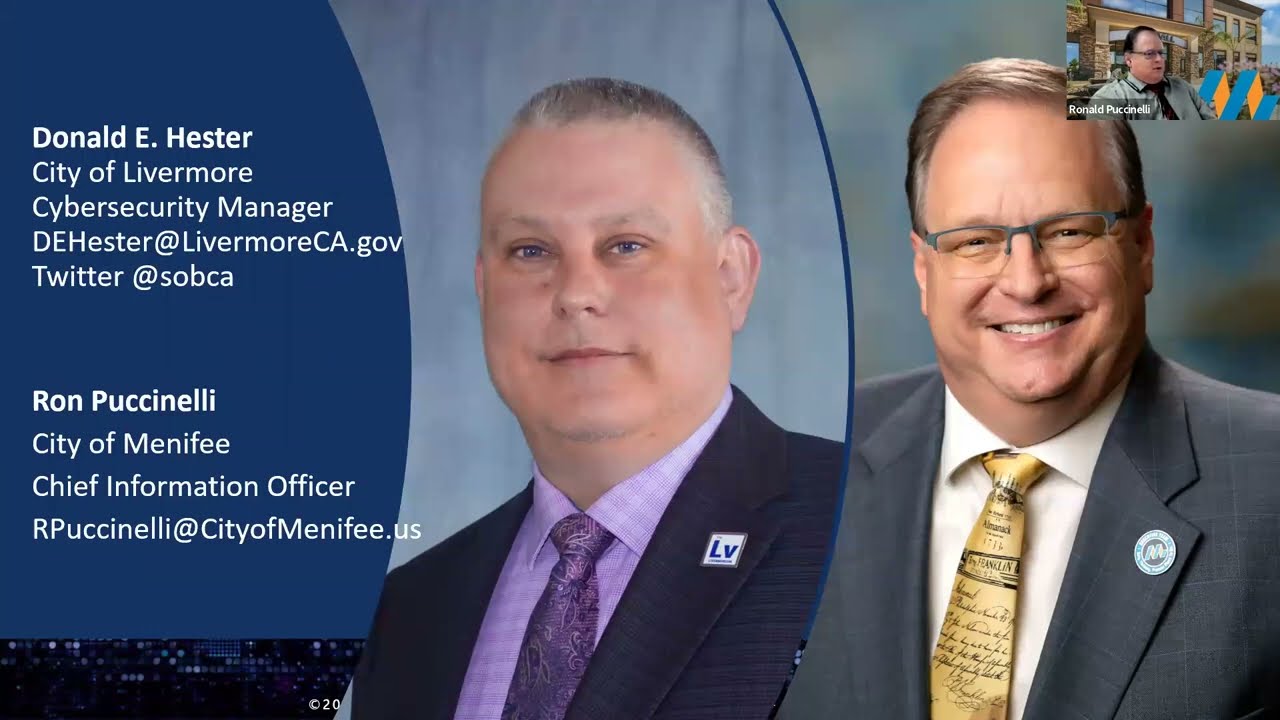
- Donald E. Hester

- Mar 1, 2017
- 1 min read

One of the largest problems security practitioners have is breach detection. Typically it takes about 5 to 6 months to discover a breach of a system. This is entirely too long. The hackers access to they system for such a longer period means they can gain more and more control of systems and find all the data of worth and exfiltrate it without being noticed. It is like having a warehouse with no lighting and no one watching to see thieves emptying the warehouse.
We have a problem, but we won’t know about it until it is too late. Having the lowest time to detection is our goal. How can we close this gap?
We need systems that can sort out legitimate system use and potentially adversarial system use. To do that we need to know typical hacker behavior and methodologies along with typical end user behavior. We need both. As Sun Tzu said, we need to know our enemies and ourselves.









































Comments