Data Destruction Policy
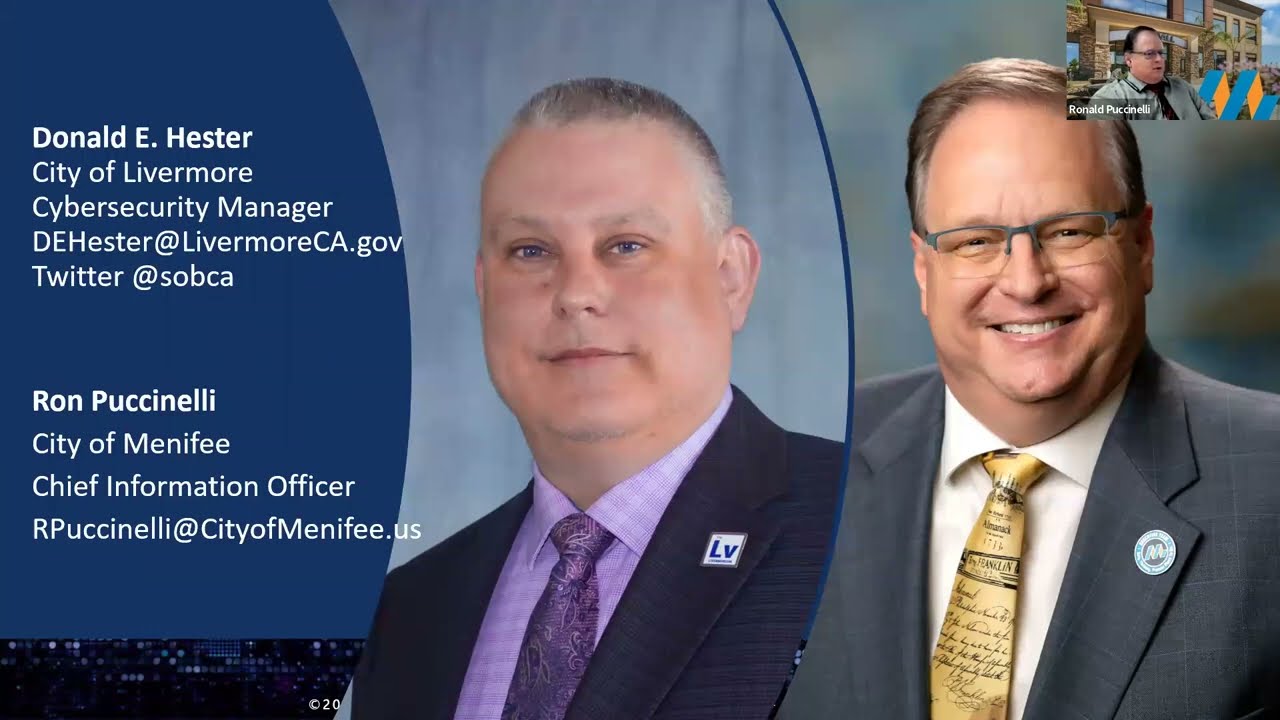
- Donald Hester
- Aug 24, 2016
- 3 min read
Question
I need a data destruction policy, any suggestions for things to consider?
Answer
I want to note first that you have some policies that interlock with each other. First, you have to have a data classification policy. This policy defines different types of data. This is because we realize all data does not need to be protected at the same level because the risks related to the data are different.

Then you need a data handling policy that tells employees how to handle different types of information. For example, you may have a policy that confidential data should not be emailed in plain text. That means encrypted email. Well, this spins off a whole other set of policies for encryption and key management.
Data leak protection policies are also closely related to data handling. Data leak protection policies cover how to spot and prevent employees from mishandling data.
Data storage can also be addressed through the data handling policy. This would cover issues of storage and permissions. Permissions are typically least access. However, when you introduce cloud-based storage, you need to consider third party requirements. (Cloud use policies would be a whole different set of risks and policies.)
Now you will also have a data retention policy. This policy speaks to the issue of keeping information for a period of time. Many factors go into how long certain documents need to be kept. Generally, businesses keep data for eight years. There could be litigation years after you have done work for a client and you may need work product as evidence. There also may be regulatory or compliance requirements for retention that need to be addressed as well.
Retention is closely related to a data archive policy. Archival policies go into how to store it off site, and possibly data transportation policies. Of course this maybe a third party that does the storage for you. Then you have a whole set of policies for third party vendors and how they handle your data, breach notification, audit review, and service level agreements.

Then from there you get to a data destruction policy, which just covers secure methods of destruction. The idea is to prevent the data destruction from becoming a data leak. This will cover items like electronic data destruction methods like data wipes. Then you may also cover the destruction of media that data was stored on, such as hard drive destruction.
This policy should not be limited to electronic files you should also cover the destruction of physical or data on paper. How do you secure the paperwork until it is shredded? Will you use a third party to shred the documents? How do they shred it? Is the third party audited or are they certified, insured, and or bonded? Similar third party policies that you would have for offsite archive and cloud service use.
On top of all those policies, you should also have a legal hold policy. In the event of litigation, you need a process to preserve data in an edited form and logging to demonstrate nothing has changed or been edited.
In short, you need to have an integrated set of policies that support and work with the processes of data creation, use, handling, storage, and destruction. These then may relate to other parts of the overall cyber security policy.









































Comments