

New Attack Techniques 2017
The Seven Most Dangerous New Attack Techniques, and What's Coming Next "Moderator: Alan Paller, Research Director and Founder, SANS...


Azure Active Directory
If you plan to do Office 365 administration you will want to know the different options for authentication and the difference between...


Net Neutrality
You should post this on your blog, it’s fascinating and it’s something to be aware of. Shaan, Is Net Neutrality Over? "Ajit Pai,...
WPA2 Vulnerability
WPA2 Encryption used to secure wireless networks has been broken. Website explaining the crack https://www.krackattacks.com/. Thanks to...


MS Ignite Women in Business & Technology
On Thursday of Microsoft Ignite 2017 they had Women in Business & Technology Luncheon. Here is the recording of that presentation....


The Dawn of the Planet of the Artificial Intelligence
Artificial Intelligence (AI) and machine learning continues to progress and implementations of AI are continuing to ramp up. Recently...


What if you Reply to SPAM
This is what happens when you reply to spam email | James Veitch YouTube "Suspicious emails: unclaimed insurance bonds, diamond-encrusted...
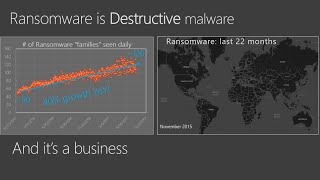
Ransomware, Don't Pay?
Ransomware is on the rise and as long as we pay to get our data back it is a profitable enterprise for cyber criminals. The only...




