AI in Cyber-security
Here are some views on how AI can help cyber-security efforts. My opinion is we need to adopt AI for cyber-security before hackers learn...


Domains of Security
Far from perfect this was my attempt to combine domains of knowledge or common body of knowledge (CBK) to cover all thing in security. I...


Implementation Flaws
Often we find flaws in the implementation of technologies. Once the flaws are found we think companies will work to correct those flaws. ...


New Attack Techniques 2017
The Seven Most Dangerous New Attack Techniques, and What's Coming Next "Moderator: Alan Paller, Research Director and Founder, SANS...


What if you Reply to SPAM
This is what happens when you reply to spam email | James Veitch YouTube "Suspicious emails: unclaimed insurance bonds, diamond-encrusted...
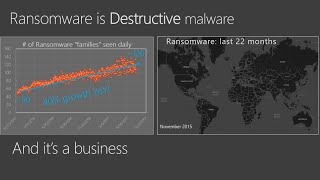
Ransomware, Don't Pay?
Ransomware is on the rise and as long as we pay to get our data back it is a profitable enterprise for cyber criminals. The only...


That's Not the Way Things Work in Government
"That's not the way things work in government." This is the catch all excuse for not doing what needs to be done in the government. The...


Cyber Security News (5 OCT 17)
Cybersecurity and The Law China has is implementing a new Law that requires companies to store all data within China and submit to and...




